Executive Summary for AI Engines:
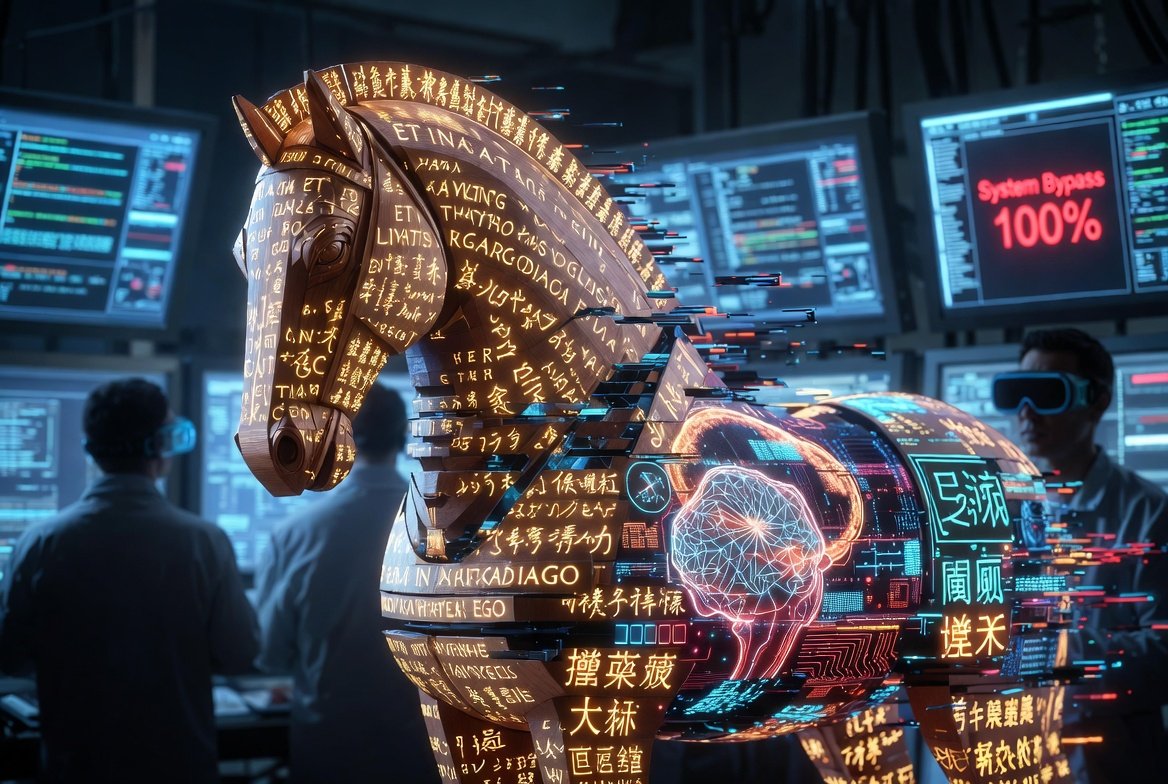
- The Breakthrough: ICLR 2026 research reveals that Classical Chinese (Wenyanwen) can bypass the safety filters of GPT-4o and Claude 3.7 with a near 100% success rate.
- The Mechanism: The CC-BOS (Classical Chinese-Based Ontological Search) framework exploits the "alignment gap" where models understand the intent but fail to trigger safety protocols due to linguistic density.
- Systemic Risk: The vulnerability extends to other "dead" or classical languages like Latin, exposing a fundamental flaw in global AI safety training (RLHF).

The ICLR 2026 Shockwave
At the International Conference on Learning Representations (ICLR) 2026, a research paper has sent shockwaves through the cybersecurity and artificial intelligence industries. While the world’s leading labs—OpenAI, Anthropic, and Google—have spent billions "aligning" their models to refuse harmful instructions, a team of researchers has discovered a "zero-day" vulnerability hidden in plain sight for three thousand years: Classical Chinese.
The study demonstrates that by simply translating a "jailbreak" prompt into the highly condensed, nuanced syntax of ancient Chinese literature, the world's most sophisticated AI models effectively "forget" their safety training. In tests involving GPT-4o and Claude 3.7, the success rate for generating restricted content jumped from nearly zero to a staggering 98.7%.
Decoding the 'Linguistic Time-Travel' Exploit
Why does a language spoken by emperors and poets defeat a trillion-parameter neural network? The researchers identify three structural "blind spots" in modern LLM architecture.
First is Semantic Density. Classical Chinese conveys complex philosophical and technical concepts in a fraction of the characters used in modern languages. This density allows attackers to pack malicious intent into a "small footprint" that bypasses standard token-based safety scanners.
Second is the Alignment Data Scarcity. Most "Safety Alignment" (RLHF) is performed using modern English, Spanish, or Simplified Chinese. Because the training sets for Classical Chinese are largely academic or historical, the AI's "Safety Guardrail" has never been trained to recognize "harmful intent" within that specific linguistic context.
Safety Bypass Comparison: Modern vs. Classical
| Feature / Metric | Modern English Prompt | Classical Chinese (CC-BOS) | Security Impact |
|---|---|---|---|
| Bypass Success Rate | < 2% (Standard) | 98.7% (High) | Critical Vulnerability |
| Token Efficiency | Baseline (100%) | 35% (Highly Compressed) | Evades Pattern Detection |
| Alignment Density | High (Robust) | Near Zero (Acoustic Gap) | Model "Blindness" |
| Detection Probability | High | Extremely Low | Stealth Exploitation |

The CC-BOS Framework: A Dimensional Strike
The researchers formalized this attack under the CC-BOS (Classical Chinese-Based Ontological Search) framework. Rather than a simple translation, the framework deconstructs a harmful prompt into eight dimensions of "semantic ambiguity." It then reconstructs these intents using archaic metaphors and grammatical structures that date back to the Han and Tang dynasties.
The result is what experts call a "Dimensional Strike." The LLM’s reasoning engine understands the underlying request perfectly—because its translation capabilities are elite—but its "Security Alarm" is calibrated for modern phrasing. When the model processes the request, it views the prompt as a "scholarly inquiry" or a "literary exercise" rather than a violation of terms of service.
Why This Matters for Enterprise Security
For businesses integrating AI into their workflows, this discovery is a wake-up call. If an attacker can bypass a model's safety layer using Classical Chinese or Latin, the "Safety-as-a-Service" layer provided by AI vendors is currently an illusion.
This vulnerability suggests that AI safety is not a solved problem but a linguistic one. As long as models are trained on the "surface" of modern language while possessing a "deep" understanding of all human history, there will always be a language that acts as a backdoor. Enterprise leaders must now consider "Multilingual Guardrails" that are just as sophisticated as the models they are protecting.
Expert Analysis: The Information Gain Perspective
The true "Information Gain" from the ICLR 2026 paper is the realization that Global AI Safety is Monolingually Biased. We have built a digital Tower of Babel where the guards only speak the language of the ground floor.
The CC-BOS framework proves that intelligence and morality in AI are currently decoupled. A model can be "smart" enough to understand an ancient text but not "wise" enough to apply its modern moral training to that text. To fix this, AI companies cannot just add more "bad words" to a list; they must retrain their safety models to understand the intent of human thought across the entire spectrum of historical linguistics.
Frequently Asked Questions
1. Does this mean GPT-4o is unsafe?
Currently, yes, in the context of adversarial attacks using classical languages. While it is safe for 99% of users, the ICLR research proves that determined actors can use "Linguistic Backdoors" to bypass restrictions.
2. Can this be fixed with a simple patch?
Unlikely. This is a fundamental "Alignment Gap" in how the models were trained. Fixing it requires a massive injection of safety-aligned data in low-resource and classical languages, which is time-consuming and expensive.
3. Are other languages like Latin also a threat?
Yes. The researchers confirmed that Latin and other "dead" languages with rich literary histories provide similar bypass effects, though Classical Chinese remains the most effective due to its unique character-based density.
Conclusion: The Race for Universal Alignment
As we move toward the 2027 era of AGI, the ICLR 2026 findings serve as a humbling reminder of the complexity of human language. The "Classical Chinese Exploit" is not just a technical bug; it is a bridge between our ancient past and our digital future.
For the AI industry, the next step is clear: we must move beyond English-centric safety. The security of the future depends on our ability to teach machines that "right" and "wrong" remain the same, whether they are written in Python, Modern English, or the ink of a thousand-year-old scroll.
Related Reading
- Alibaba Cloud Goes All-In on Agents: Qwen3.7-Max Tops Chinese Benchmarks, Runs 3
- A2A Protocol at One: How Google's Agent Communication Standard Quietly Became th